Our products
Our hardware and software IoT security solutions make scaling devices easy and safe for faster time to market.
Q:Architecture™ provides scalable IoT security with the most resilient approach
Q:Architecture™ is a security architecture of two products that work independently and together to increase security, unlock scale and drive revenue opportunities…
- QDID™ — a quantum-driven hardware root-of-trust that generates unique, unforgeable identities and cryptographic keys on demand.
- QuarkLink™ — a universal IoT security platform that lets device owners manage their IoT ecosystem security with ease.
You need hardware and software working together for genuinely secure and scalable device security. Get your IoT system fully secured with Q:Architecture.
Easy IoT security solutions from chip to cloud
Full end-to-end security of your IoT devices isn’t just a risk mitigator. Better secured IoT devices can unlock new business opportunities and revenue streams.
Zero touch, zero trust
The assignment of unique device identities and all three IoT device deployment stages (provisioning, onboarding, monitoring) are fully automated and secure. Zero-trust means you don’t have to rely on any third parties in your supply chain to secure devices.
Extensible security
Our IoT security platform QuarkLink works with any hardware root-of-trust. This means MCUs, ASICs and other devices can be easily integrated and protected. Adopt a chip-to-cloud architecture that easily secures your whole IoT device ecosystem.
New avenues to grow
Whether you start with QDID or QuarkLink, or choose both together for the most resilient security system, IoT device security is yours to access. Accelerate your products’ time to market and open up new revenue streams from IoT service models.
Futureproof security
Other PUFs are vulnerable to hacking, counterfeiting and side-channel attacks. Because Q:Architecture harnesses a quantum phenomenon and provides multiple, uncorrelated keys, it can protect IoT devices from even the most powerful quantum computers of the future.
Unlock innovation in your IoT ecosystem
Scalable IoT security made easy and end-to-end. Get more insight from one of our experts.
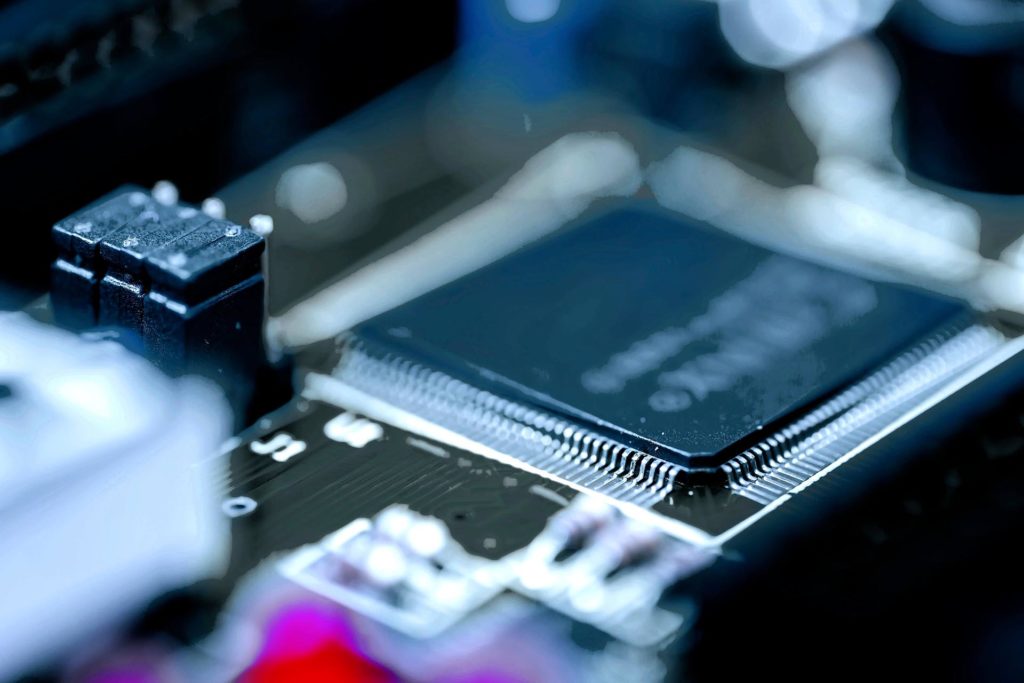
QDID™
The world’s first quantum-driven hardware root-of-trust is the most secure in the industry. QDID generates on-demand, unforgeable cryptographic keys based on silicon’s physical properties to give your IoT devices unique identities and cryptographic keys.
QuarkLink™
Our universal IoT security platform integrates with any root-of-trust and manages zero-touch provisioning, onboarding and security management of your IoT devices. QuarkLink unlocks scale for faster time to market.

Get more secure with Q:Architecture™
With security sorted, you can explore new horizons with your IoT devices. Talk to our team for more information.
